Autonomous OSINT Investigations. Certainty Delivered.
Point Axiom Intel at a target and get a structured intelligence brief — entities mapped, relationships discovered, gaps identified, sub-investigations spawned automatically. Hours, not weeks.
How It Works
You define the question. Axiom Intel finds the answer.
Set an Intelligence Goal
Name a target entity and define your intelligence question. Use AI-assisted goal refinement to sharpen the objective. Four quick-start templates: Corporate Investigation, Person of Interest, Domain/Infrastructure, Financial Network.
The Investigation Engine Runs
Choose Quick, Standard, or Thorough mode with configurable cycles. The platform autonomously generates search strategies, collects from multiple sources through encrypted proxy chains, normalizes entities with AI, discovers relationships, and identifies intelligence gaps — spawning sub-investigations to fill them.
Get Your Scored Brief
Receive a versioned executive summary with a 0–100 certainty score that tracks across brief versions, an entity graph, relationship map, and identified gaps. Export as PDF. Deliver to your client.
Built for Serious Investigations
Autonomous Intelligence Cycle
Search → collect → normalize → relate → summarize → identify gaps → spawn sub-investigations. The Investigation Engine runs the full intelligence cycle unattended while you work on other things.
Isolated Infrastructure
Every customer gets their own dedicated server with rotating proxy pool and encrypted database. Your investigation data never touches another customer's infrastructure.
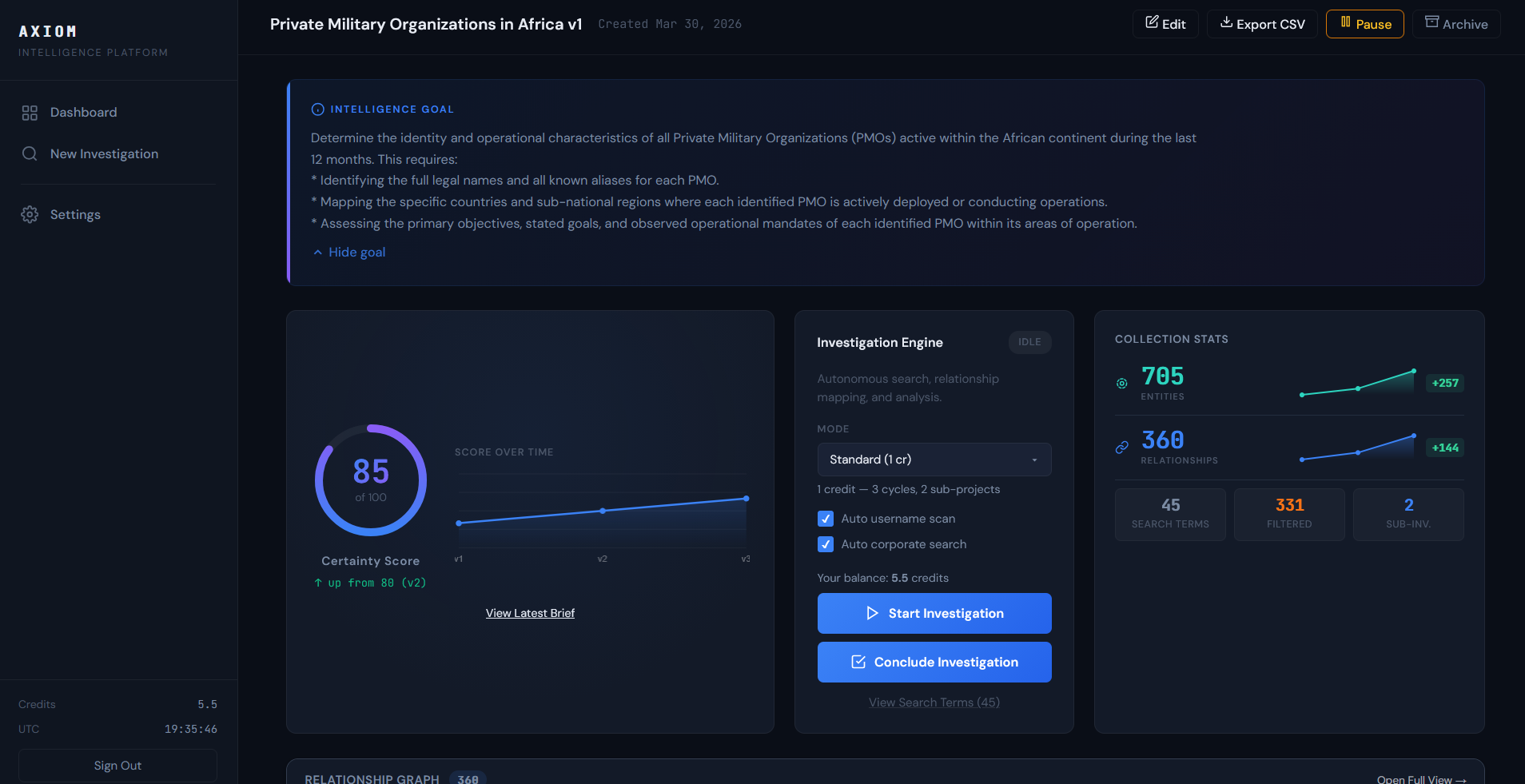
Certainty Scoring
Every investigation produces a 0–100 certainty score displayed as a ring chart that tracks across brief versions. See exactly how comprehensively your intelligence question has been answered. No other tool does this.
Multi-Source Collection
URL Collector, Search & Scan across news and web engines, Username Scan across 400+ platforms, and Corporate Registry Search via custom corporate registry scanner — all automated, all routed through your isolated infrastructure.
AI Relationship Discovery
Zero-cost attribute clustering (shared tracking IDs, certificates, email domains) followed by AI-powered relationship mapping. Discovers connections humans miss.
Executive Summaries
Versioned intelligence briefs in structured format: BLUF, key findings, entity overview, relationship analysis, assessment, gaps, and recommended next steps. Export as PDF or CSV.
Ready to see what autonomous OSINT can do for your investigations?
See the Platform
Real screenshots from a live investigation.
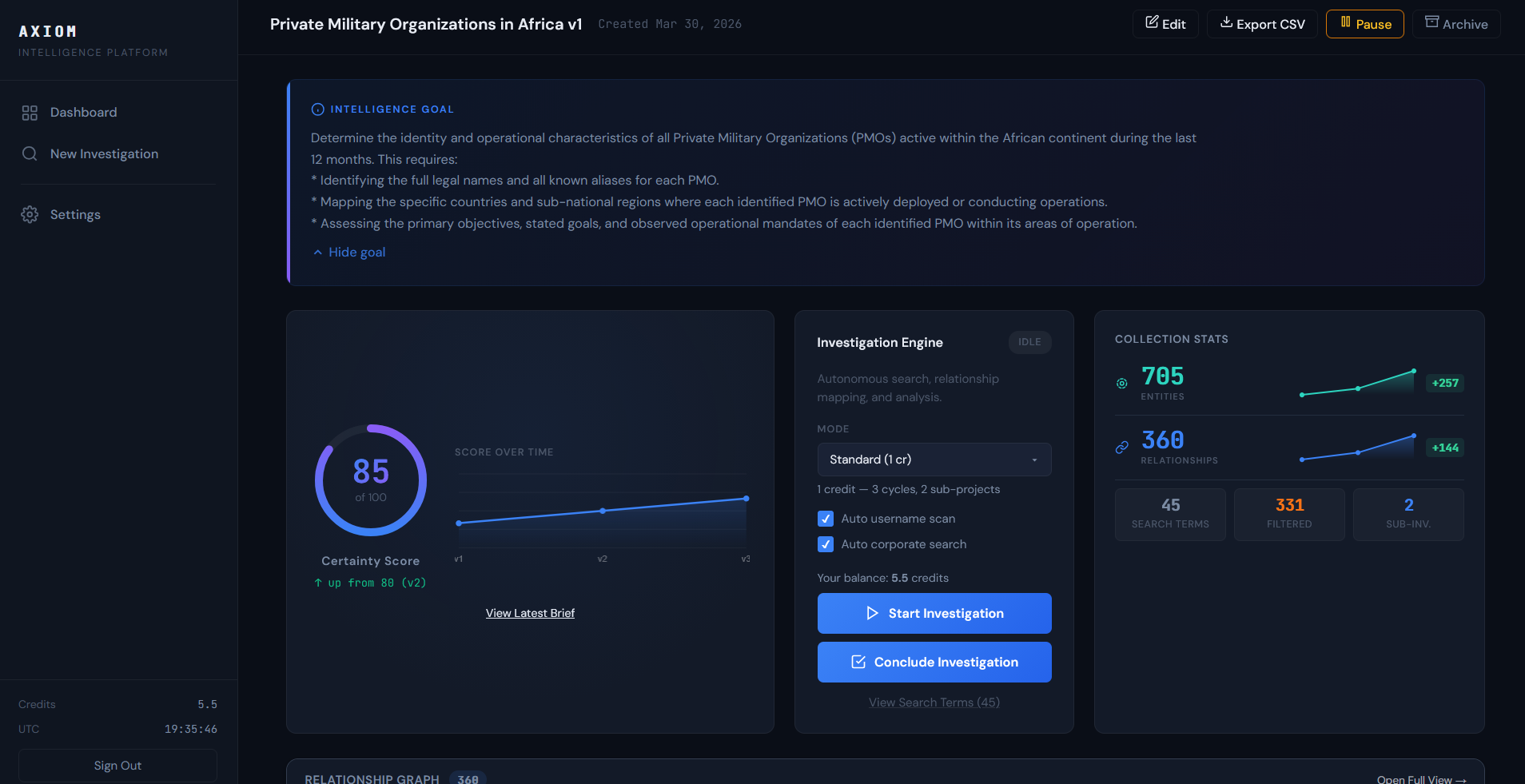
Investigation Command Center
Monitor an autonomous investigation from goal to scored brief. Watch entities, relationships, and certainty score update in real time -- no manual intervention needed.
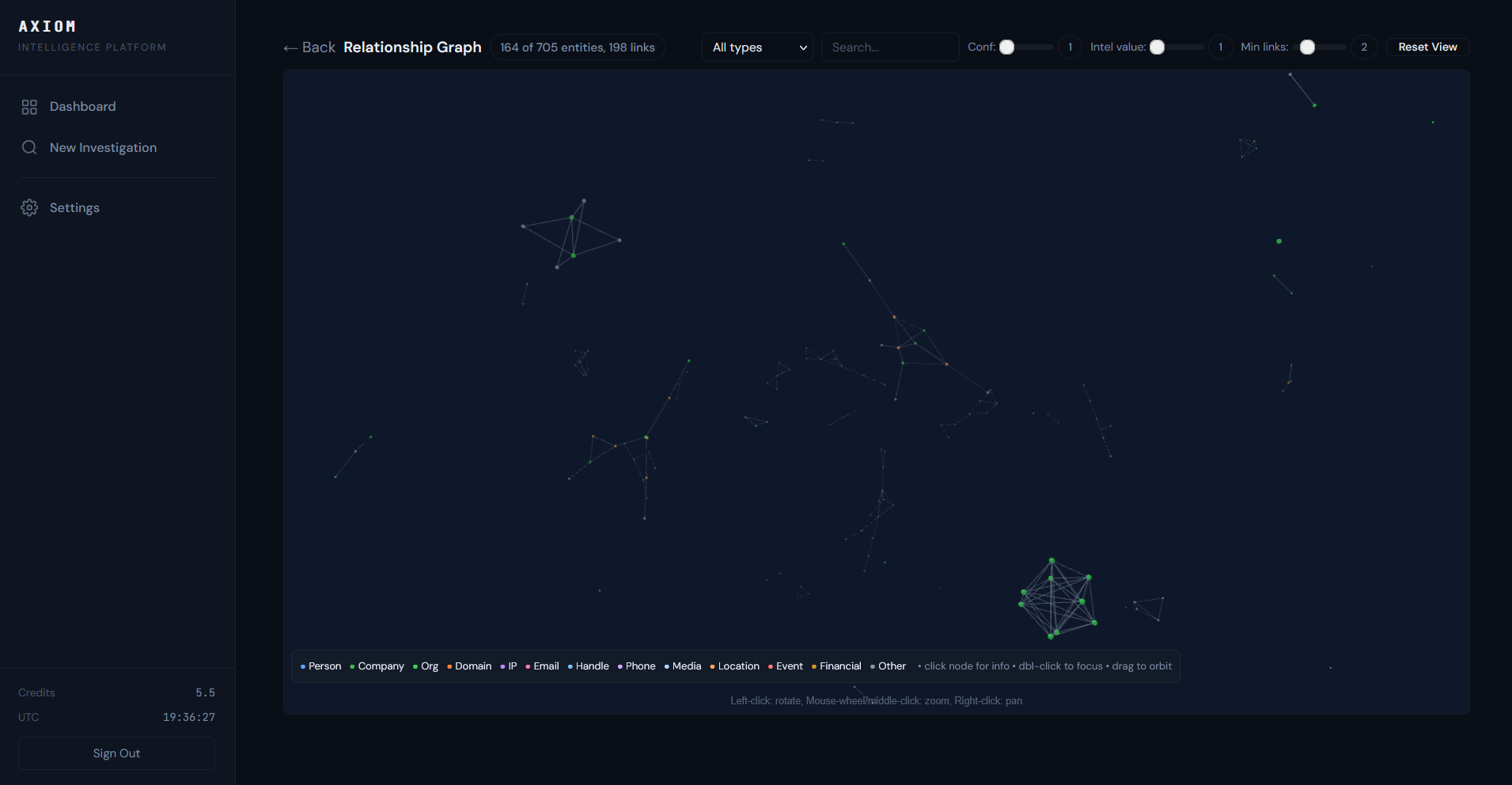
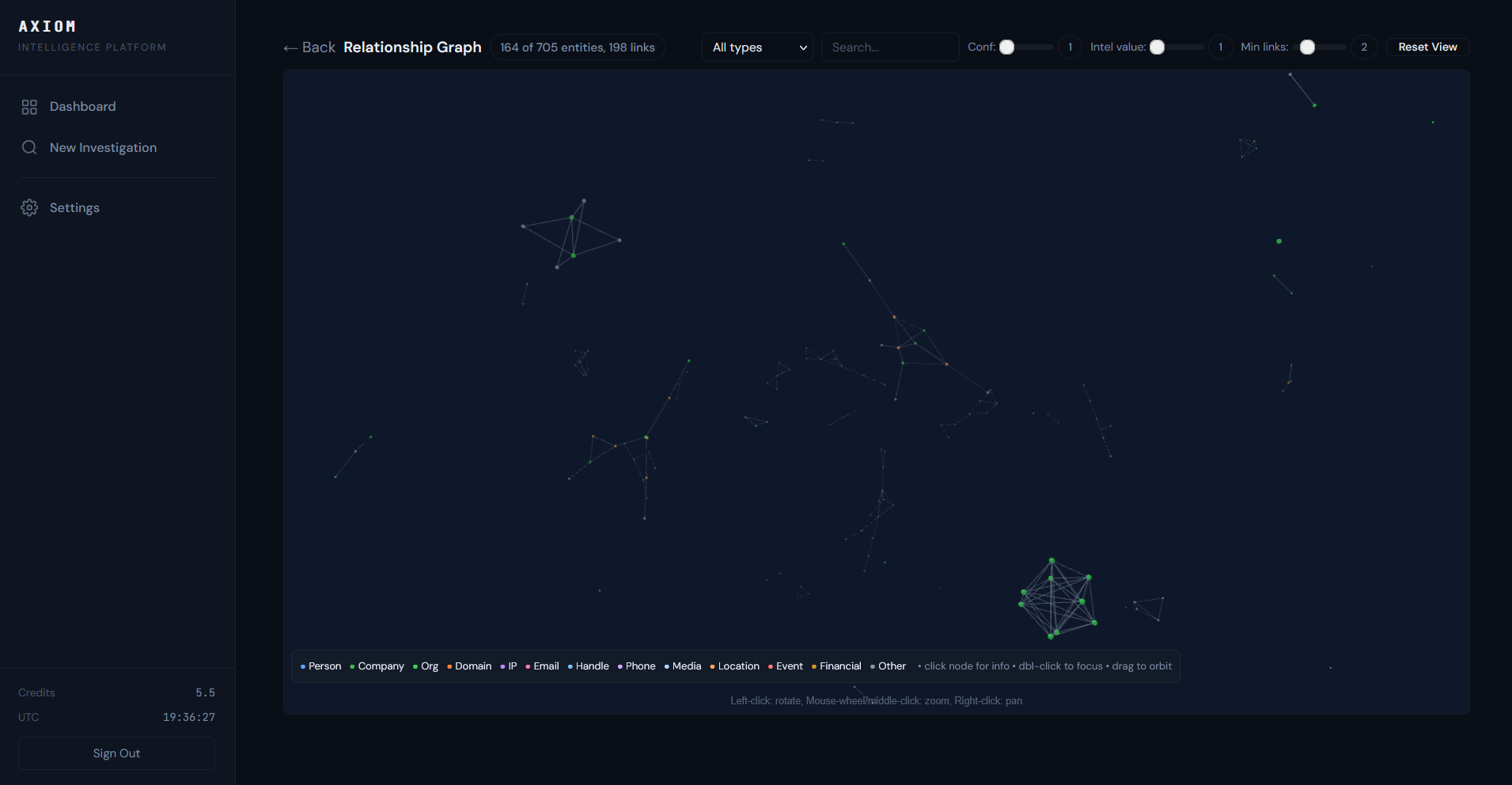
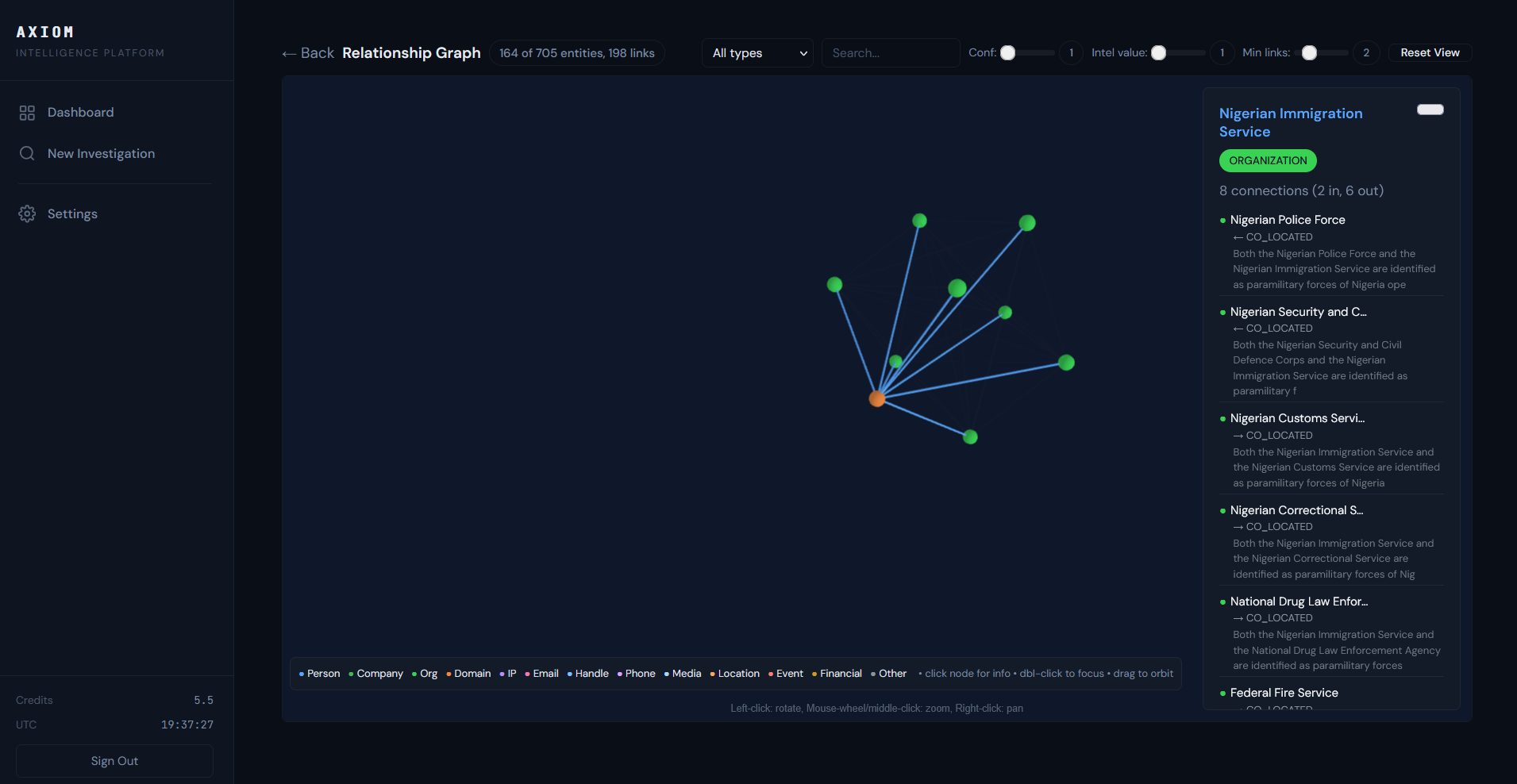
Relationship Graph
See every connection the engine discovers. Click any entity to trace relationships, view attributes, and verify against source URLs.
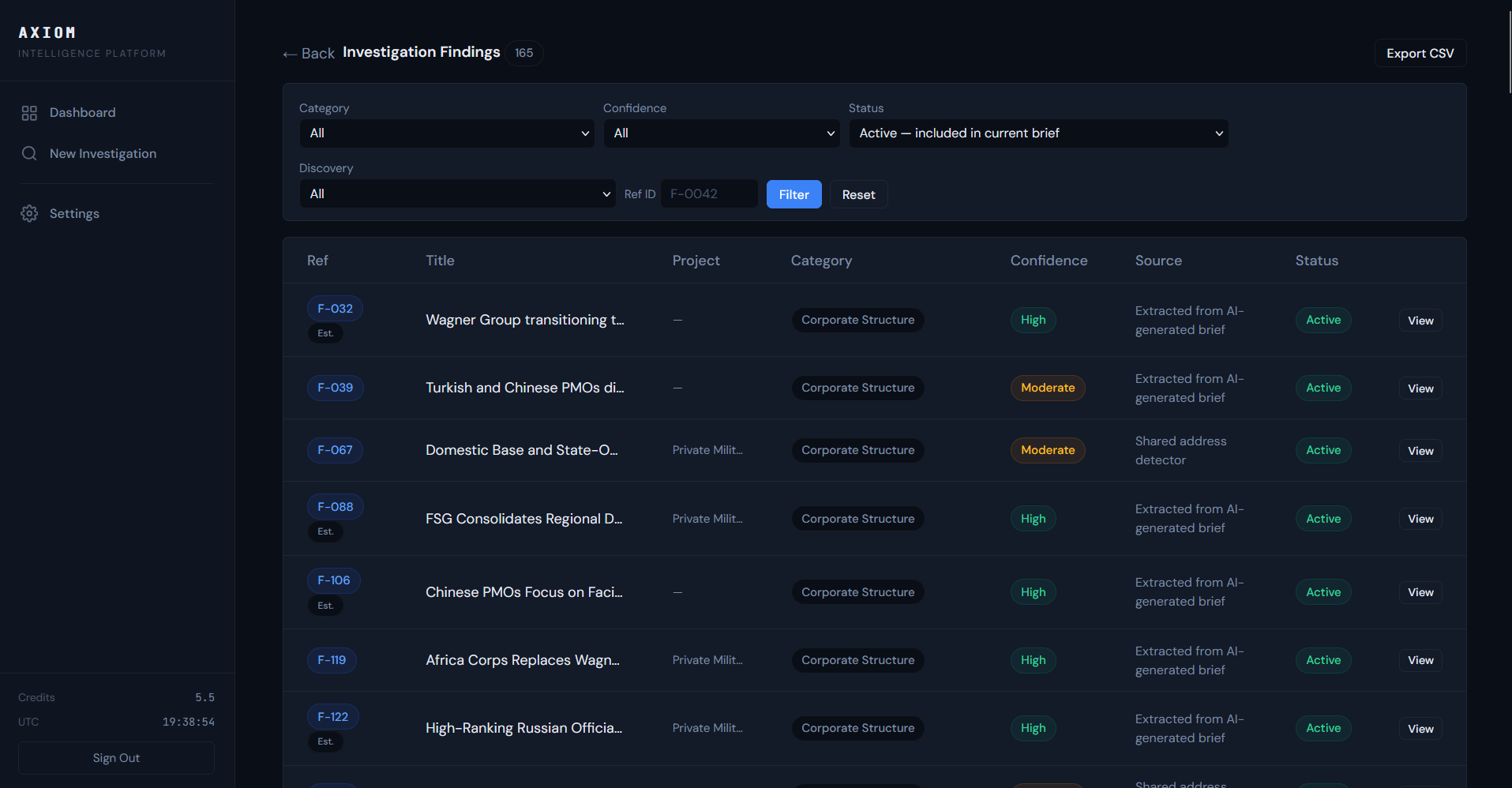
Investigation Findings
Every finding carries a confidence score and cites specific open sources. Verify any claim independently -- no black boxes.
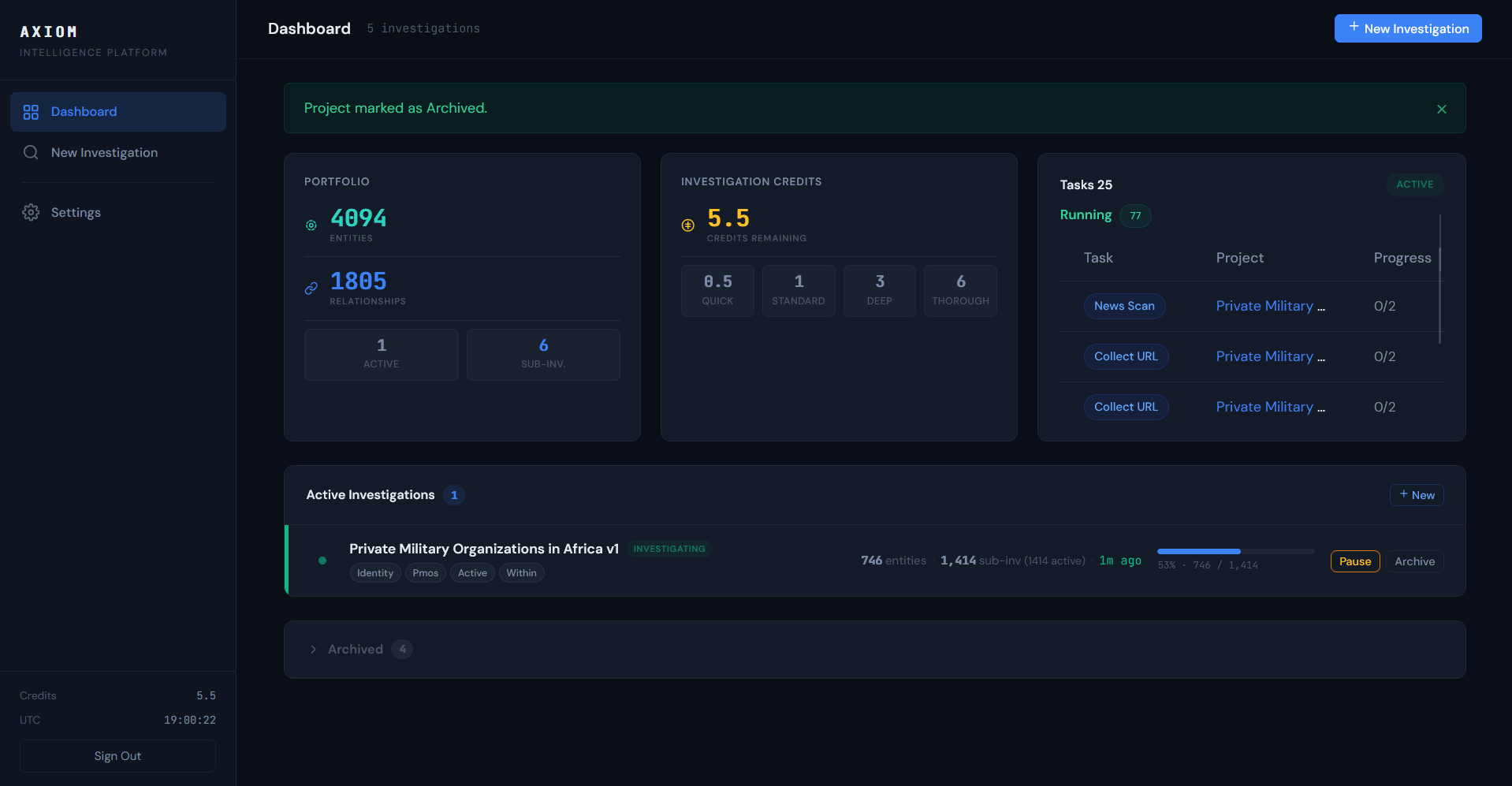
Dashboard
Track your full investigation portfolio -- entities collected, credits remaining, active investigations, and results delivered. All in one view.
Choose Your Plan
Every plan includes a dedicated isolated server, proxy rotation, and full platform access. Your credentials are delivered within 15 minutes of payment.
A single due diligence engagement from a consulting firm runs $5,000–$25,000 and takes weeks. Your first Axiom investigation delivers a scored brief in under 3 hours.
Starter
For independent investigators, journalists, and solo analysts
Best for solo investigators & journalists
- Dedicated isolated server
- 3 concurrent investigations
- Standard depth (5 cycles)
- $5/mo AI budget included
- Email support (24hr response)
Professional
Best for security teams & due diligence firms
For teams that need depth — sub-investigations, continuous monitoring, and priority support
- High-performance dedicated server
- 10 concurrent investigations
- Deep + Continuous modes
- $15/mo AI budget included
- Priority support (12hr response)
- Sub-investigation spawning
Enterprise
For government agencies, regulated firms, and custom deployment requirements
Best for government & regulated industries
- Dedicated high-capacity infrastructure
- Unlimited investigations
- Custom AI budget allocation
- API access for integration
- SLA with dedicated support
- Custom data retention policies
All plans include: rotating proxy pool, encrypted database, automated daily backups, and full data export.
AI overages billed at cost + 20%. Cancel anytime. 30-day data retention on cancellation.
Not sure which plan fits? Tell us about your use case and we'll recommend the right setup.
Already a subscriber?
Need more investigation capacity? Purchase credit packs for your existing instance.
The Question
A security analyst needed to identify and map the financial, logistical, and operational networks connecting three state-affiliated private military organizations operating across the Sahel, Central Africa, and the Middle East -- including shell companies, proxy directors, front entities, financial intermediaries, and sanctions-evasion structures spanning multiple jurisdictions.
What Axiom Intel Did
The analyst entered a goal statement describing the three organizations and their suspected areas of operation. The platform autonomously generated 83 search strategies, collected from corporate registries, news archives, sanctions databases, and public records across multiple countries, and produced 5 progressively refined executive briefs as new intelligence emerged -- each with an updated certainty score tracking what had been answered and what remained unknown.
Investigation Depth
What It Found
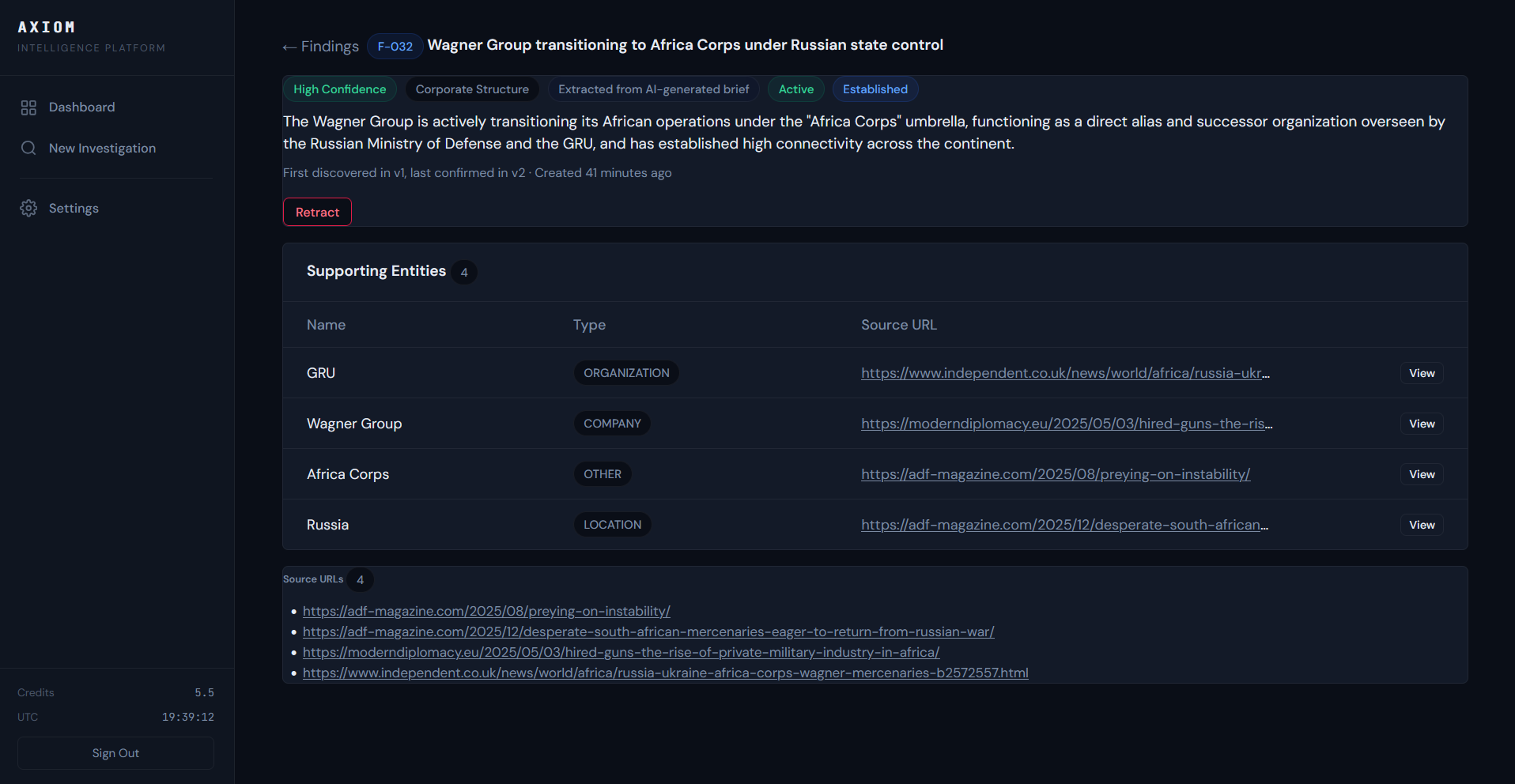
Cited, Verifiable Findings
Every finding in an Axiom investigation carries an in-text citation reference (e.g., [F-031]) that appears directly in the executive brief. Click any reference to see the full finding detail -- including the supporting entities, confidence level, category, discovery method, and every source URL used to establish it.
This means every claim in the brief is traceable back to specific open sources. Analysts can verify findings independently, assess confidence, and identify which sources contributed to each conclusion. No black boxes.
Axiom Intel autonomously mapped the full operational architecture of Russian, Chinese, South African, and Turkish private military organizations across Africa -- identifying 74 alias relationships connecting front entities to successor organizations, 129 co-location links revealing shared operational bases, and 33 ownership chains tracing corporate control structures. The platform confirmed the Wagner Group's formal transition into the Africa Corps under GRU control, mapped Frontier Services Group's acquisition strategy consolidating Chinese PMO dominance in East Africa through Hong Kong financial channels, and traced the Dyck Advisory Group's counter-insurgency deployments across Cabo Delgado -- all in 2.2 hours of autonomous operation.
This investigation ran autonomously in 2.2 hours. Ready to run your own?
Intelligence Gaps Identified
The investigation reached 85/100 certainty. The platform identified what it could not answer from open sources -- including sealed corporate registry filings in two US states, undisclosed executive officers behind offshore holding structures, and specific transactional evidence (SWIFT data, bills of lading) linking mine output to specific refineries. These gaps were documented with recommended collection methods for human follow-up.
Private Military Organizations in Africa V1
Executive Intelligence Summary
UNCLASSIFIED // FOR OFFICIAL USE ONLY
Operational Baseline of Private Military Organizations (PMOs) in Africa (Trailing 12 Months)
Open-source intelligence confirmed that the African private military landscape over the last 12 months was dominated by Russian, Chinese, South African, and Turkish entities, each operating with distinct state-aligned or commercial mandates. The investigation successfully mapped the legal names, alias networks, and specific sub-national deployments of these PMOs, revealing that Russian forces prioritized regime survival and resource extraction in the Sahel, Chinese firms focused on Belt and Road Initiative (BRI) infrastructure protection in East Africa, and South African groups engaged in commercial counter-insurgency. Certainty Score: 85/100
Extensive entity object expansion (over 10%) and the resolution of OSINT sub-project gaps regarding specific sub-national deployment zones for the Africa Corps and Chinese PMOs justified a high-confidence assessment, though precise tactical troop counts and specific financial contracts remained partially obscured.
Key Findings
- Russian MoD Assimilation of Wagner: The Russian state formally transitioned the Wagner Group [F-031] into the “Africa Corps” under the direct operational control of the Russian Ministry of Defense and military intelligence (GRU) [F-032], [F-119]. Africa Corps maintained an extensive operational footprint across the Sahel and Central Africa [F-034], specifically deploying to Ouagadougou and Loumbila in Burkina Faso [F-114], as well as Niamey, Mali, and the Central African Republic (CAR) [F-010].
- Chinese PMO Consolidation in East Africa: Chinese PMOs [F-012] significantly expanded their footprint to protect state-owned assets and BRI infrastructure, prioritizing facility protection over combat [F-106]. Frontier Services Group (FSG) consolidated regional dominance by acquiring Beijing DeWe Security Service and Kenyan aviation assets [F-088], utilizing Hong Kong as a financial hub [F-064], [F-093] and Nairobi as a forward operational base [F-069].
- South African Commercial Counter-Insurgency: South Africa continued to serve as a vital historical and contemporary hub for PMO logistics [F-014]. The highly connected Dyck Advisory Group (DAG) [F-027], [F-077] extensively leveraged this infrastructure to conduct active deployments in Mozambique [F-037], specifically operating in Cabo Delgado hubs including Macomia [F-083], Pemba [F-084], and Maputo [F-085] to counter Ansar al-Sunna insurgents [F-139].
- High-Activity Geographic Nexus Zones: The Democratic Republic of the Congo (DRC) functioned as a highly concentrated operational hub for multiple competing mercenary networks [F-030]. Similarly, North East Mali emerged as a critical conflict node where Russian forces repeatedly engaged insurgent coalitions [F-156].
- Turkish PMO Structuring: SADAT International Defense Consultancy rapidly structured its corporate entities in Turkey to facilitate international military consulting and operations [F-013], [F-141].
Entity Overview
| Entity Category | Key Organizations & Aliases | Operational Jurisdiction & Sub-National Bases | Primary Observed Mandate |
|---|---|---|---|
| Russian State PMOs | Africa Corps, Wagner Group, Redut, Convoy, M Invest, Bear Brigade | Burkina Faso (Loumbila, Ouagadougou), Niger (Niamey), Mali (Aguelhok), Sudan, CAR | Regime survival, proxy warfare, resource extraction (Nordgold) |
| Chinese PMOs | Frontier Services Group (FSG), Beijing DeWe Security Service, Huaxin Zhong An | Kenya (Nairobi), Djibouti, DRC, Tanzania, Zambia | BRI infrastructure defense, asset protection for State-Owned Enterprises |
| South African PMOs | Dyck Advisory Group (DAG), Executive Outcomes, Paramount Group, Umbra Aviation | Mozambique (Cabo Delgado, Macomia, Pemba), South Africa | Direct combat, counter-insurgency, aviation logistics |
| Turkish PMOs | SADAT Defense Consultancy, Akademi Sancak | Turkey, Somalia, Libya, Horn of Africa | Military consulting, host-nation force training |
| Host/Adversary Actors | Alliance of Sahel States (AES), RSF, JNIM, ISGS, Ansar al-Sunna | Sahel region, Sudan (Darfur), Mozambique | Insurgency, host-nation agreements, localized conflict |
Relationship Map (Narrative)
The architecture of PMOs in Africa relied heavily on complex alias networks, state-sponsorship, and shared physical infrastructure. Russian mercenary operations were fully subordinated to the Russian Ministry of Defense. GRU officials, prominently Deputy Defense Minister Yunus-bek Yevkurov [F-115] and General Andrey Averyanov [F-122], directly negotiated host-nation agreements with junta leaders like Ibrahim Traoré (Burkina Faso) and Abdourahamane Tiani (Niger) to base Africa Corps personnel. These deployments were financially sustained through overlapping corporate networks tied to Russian resource extraction entities, notably Nordgold in Burkina Faso. An operational correlation was also verified in Sudan, where the Russian-linked M Invest shared geographic footprints with the Rapid Support Forces (RSF) [F-017].
Chinese operations demonstrated deep alignment with the Chinese Communist Party’s strategic goals but operated distinctly from Russian kinetic forces. FSG, financially backed by the state-owned CITIC Group, absorbed regional competitors to protect China National Petroleum Corporation (CNPC) assets and BRI railways. Hua Xin Zhong An (HXZA) operated in Djibouti in close geographic coordination with the People’s Liberation Army (PLA) Support Base, illustrating a formalized civil-military integration.
In the commercial sector, the South African PMO ecosystem was driven by legacy networks, with Executive Outcomes [F-028] and WatchGuard [F-018] historical frameworks influencing modern outfits. The Dyck Advisory Group (DAG) was contracted directly by the Mozambican government and corporate entities (TotalEnergies) to provide combat aviation support against the Islamic State’s Central Africa Province and Ahlu Sunnah Wa-Jama in Cabo Delgado, acting as a force multiplier for local militaries. Think tanks and policy institutes like CSIS [F-020] actively monitored these complex networks to assess their impact on regional stability.
Assessment
With high confidence, the deployment of Private Military Organizations across Africa has fractured into two distinct models: state-subsidized strategic proxy forces (Russia, China, Turkey) and commercial kinetic contractors (South Africa). The absorption of Wagner into the Africa Corps represents a formalization of Russian hybrid warfare designed to outcompete Western influence while securing mineral rights. Chinese PMOs will likely continue expanding their footprint, operating strictly defensively to secure economic supply chains without engaging in host-nation internal conflicts. African states facing critical insurgencies (e.g., Mozambique, DRC) will likely continue procuring commercial PMOs like DAG to bridge tactical shortfalls in their national militaries.
Intelligence Gaps
- Specific financial compensation parameters and the exact values of resource concessions granted to Nordgold and other Russian shell companies funding the Africa Corps.
- The precise tactical deployment numbers and kinetic capabilities of Chinese PMO personnel at specific BRI infrastructure nodes.
- Comprehensive corporate records mapping the remaining decentralized alias networks of former Wagner entities that have not formally integrated into the Africa Corps.
- Signals intelligence (SIGINT) regarding the command and control communications between GRU handlers in Moscow and Africa Corps forward operating bases in Loumbila and Niamey.
- Human intelligence (HUMINT) detailing the coordination protocols between Chinese PMO leadership (FSG/HXZA) and the PLA Support Base in Djibouti.
- Classified satellite imagery analysis of the physical security postures and vehicle complements at Africa Corps headquarters in Ouagadougou.
Recommended Next Steps
- Targeted Financial Tracking: Execute a deep-dive corporate records and financial ledger analysis of Nordgold and associated Russian mining fronts in Burkina Faso and the CAR to map the Africa Corps compensation structure.
- Corporate Network Monitoring: Continuously monitor Hong Kong [F-064] and Turkish trade registries to identify newly formed subsidiaries under FSG and SADAT [F-141] that may obscure future deployments.
- Geospatial Profiling: Task commercial and open-source satellite imagery analysis on known Africa Corps facilities in Loumbila and Niamey, as well as Chinese logistics hubs in Nairobi, to establish baseline personnel and equipment counts.
Contact Us
For enterprise pricing, government procurement, or custom deployment requirements.
Email us directly at [email protected] or use the form below.
Documentation & Support
Guides for getting started and getting help with your Axiom Intel instance.
Getting Started
Your instance is provisioned automatically after payment. This guide covers logging in, creating your first investigation, setting an intelligence goal, and understanding results.
Read Guide →Security Architecture
How your dedicated instance is isolated: rotating proxy pool, encrypted database, automated backups, and data retention policies.
Read Guide →Support
Contact support for technical issues, billing questions, or feature requests. Starter: 24hr response. Professional: 12hr response. Enterprise: SLA-bound.
Contact Support →Frequently Asked Questions
Common questions about Axiom Intel.
Getting Started
From payment to your first intelligence brief
1. Account Provisioning
After completing payment, your dedicated Axiom Intel instance is provisioned automatically. Within 15 minutes, you will receive an email at the address used during checkout containing:
- Your instance URL (a dedicated server exclusively for your account)
- A one-time setup link to create your password
Click the setup link, choose a password, and you are in. Your instance is fully isolated -- no other customer can access your server, data, or investigations.
2. Creating Your First Investigation
From the dashboard, click New Investigation. You will be guided through three steps:
Project Setup
Name your investigation and optionally add tags for organization. The name should describe the target or topic (e.g., "Wagner Group Africa Operations" or "Acme Corp Due Diligence").
Intelligence Goal
Define what you want to know in plain language. Be specific about the entities, relationships, and jurisdictions you care about. Use the AI-assisted goal refinement to sharpen your objective -- the platform will suggest improvements to maximize investigative coverage.
Review & Launch
Choose your investigation mode (Quick, Standard, Deep, or Thorough) based on how comprehensive you need the results to be. Each mode consumes a different number of credits. Review your goal and launch the investigation.
3. Investigation Modes
Each mode balances speed, depth, and credit cost:
- Quick (0.5 credits) -- 2 collection cycles, 1 sub-project. Best for rapid background checks and single-entity lookups.
- Standard (1 credit) -- 3 cycles, 2 sub-projects. The default for routine due diligence and corporate profiling.
- Deep (3 credits) -- 5 cycles, 3 sub-projects, depth 2. For complex investigations requiring network mapping and cross-jurisdictional analysis.
- Thorough (6 credits) -- 10 cycles, 5 sub-projects, depth 2. Maximum coverage for deep-dive research across multiple jurisdictions.
4. Monitoring Progress
Once launched, the Investigation Engine runs autonomously. You can monitor progress in real time from the project page:
- Certainty Score -- a 0-100 ring chart that tracks how comprehensively your intelligence question has been answered
- Collection Stats -- entity count, relationship count, and source processing metrics updated live
- Task List -- see what the engine is doing right now (collecting, normalizing, analyzing, generating briefs)
- Relationship Graph -- watch the entity network form as new connections are discovered
You do not need to keep the page open. The investigation runs on your dedicated server and you can return at any time to check status.
5. Reviewing Results
When the investigation completes, you will find:
- Executive Brief -- a structured intelligence summary with BLUF, key findings, entity overview, relationship analysis, assessment, intelligence gaps, and recommended next steps. Each brief is versioned and scored.
- Investigation Findings -- discrete findings with reference IDs, confidence levels, categories, and source attribution
- Intelligence Objects -- all discovered entities (persons, companies, organizations, locations, domains, etc.) with attributes and source URLs
- Relationships -- mapped connections between entities with confidence scores
- Relationship Graph -- interactive force-directed visualization of the entire entity network
6. Exporting
Export your results in multiple formats:
- PDF -- the executive brief formatted as a professional intelligence report
- CSV -- entity and relationship data for import into your own analysis tools
Security Architecture
How your investigations are protected
Dedicated Single-Tenant Infrastructure
Every Axiom Intel customer receives their own dedicated server instance. Your server is not shared with any other customer. Your investigation data, collected content, AI-generated analysis, and configuration are stored exclusively on your instance. No data commingling occurs at any level.
Network Security
- Rotating proxy pool -- collection traffic is distributed across a rotating pool of proxies, preventing source sites from correlating requests back to your instance.
- TLS encryption -- all data in transit between your browser and the service is encrypted using TLS 1.2 or higher.
- Firewall rules -- access is restricted to necessary ports only. SSH is key-based (no password authentication).
Data Encryption
- Secrets at rest -- API keys and other sensitive configuration data are encrypted using Fernet symmetric encryption derived from a per-instance secret key.
- Database credentials -- generated per-instance and not shared across any infrastructure.
- Passwords -- hashed, never stored in plaintext.
Backups
Automated daily database backups are stored in encrypted object storage in a separate account from your server instance. Backups are retained for 30 days and then permanently deleted. Backup storage is encrypted at rest by the storage provider.
Data Retention
- Active accounts -- data retained on your dedicated instance for the duration of your subscription.
- After cancellation -- instance and all data retained for 30 calendar days to allow data export. After 30 days, the instance and all associated data are permanently and irreversibly destroyed.
- Backups -- retained for 30 days, then permanently deleted.
Access Control
Access to your dedicated instance is restricted to:
- You -- through the web interface using your account credentials.
- Authorized personnel -- only for infrastructure-level maintenance. We do not access, review, or analyze the content of your investigations without explicit written permission.
Third-Party Processing
Investigation text is sent to Google Gemini API for AI analysis. Your personal account information is not sent to Google. Web traffic is routed through commercial proxy providers who see destination URLs and traffic volume, but not investigation context or your identity. Payment data is processed by Stripe.
Support
Getting help with your Axiom Intel instance
Contact Support
For technical issues, billing questions, or feature requests, email us at [email protected]. Include your instance URL and a description of the issue.
Response Times
Starter Plan
Email support with 24-hour response time during business days.
Professional Plan
Priority email support with 12-hour response time, including weekends.
Enterprise Plan
SLA-bound support with dedicated response commitments defined in your service agreement.
Billing & Account
Manage your subscription, update payment methods, and view invoices through the Stripe Customer Portal. Access it from your account settings within the platform, or contact [email protected] for assistance.
Enterprise Inquiries
For government procurement, custom deployment requirements, API access, or volume licensing, contact our sales team.
Investigation Credits
Credits fuel your investigations. Each time you launch an investigation, credits are deducted based on the depth and complexity of the mode you choose. Purchase credit packs for your existing Axiom Intel instance.
What Credits Buy
| Mode | Credits | Cycles | Sub-Projects | Max Depth | Best For |
|---|---|---|---|---|---|
| Quick | 0.5 | 2 | 1 | 1 | Rapid background checks, single-entity lookups |
| Standard | 1 | 3 | 2 | 1 | Routine due diligence, corporate profiling |
| Deep | 3 | 5 | 3 | 2 | Complex investigations, network mapping |
| Thorough | 6 | 10 | 5 | 2 | Deep-dive research, multi-jurisdiction tracing |
10 Credits
For periodic investigations and ad-hoc research
- 10 investigation credits
- 10 standard or 20 quick investigations
- No expiration
- Use any investigation mode
25 Credits
For active investigators running regular cases
- 25 investigation credits
- 25 standard or 8 deep investigations
- No expiration
- Use any investigation mode
75 Credits
For teams and high-volume investigation work
- 75 investigation credits
- 75 standard or 12 thorough investigations
- No expiration
- Use any investigation mode
Credits are added to your account instantly after payment. No expiration.
Need a subscription with included credits? View subscription plans
Terms of Service
Axiom Intelligence Platform — Effective Date: March 29, 2026
1. Agreement to Terms
These Terms of Service (“Terms”) constitute a legally binding agreement between you (“Customer,” “you,” or “your”) and Innovative Technology and Consulting Solutions LLC (“Company,” “we,” “us,” or “our”), governing your access to and use of the Axiom Intelligence Platform platform, including all associated software, services, APIs, and documentation (collectively, the “Service”).
By creating an account, accessing the Service, or making a payment, you acknowledge that you have read, understood, and agree to be bound by these Terms and the Acceptable Use Policy incorporated herein by reference. If you are entering into these Terms on behalf of an organization, you represent and warrant that you have the authority to bind that organization to these Terms.
If you do not agree to these Terms, you must not access or use the Service.
2. Description of Service
Axiom Intelligence Platform is an AI-powered open-source intelligence (OSINT) investigation platform. The Service automates the collection, normalization, analysis, and synthesis of publicly available information from the internet. The Service operates on a managed single-tenant architecture, providing each Customer with a dedicated, isolated server instance.
The Service uses artificial intelligence models provided by third-party providers (including but not limited to Google Gemini) to process and analyze collected data. The Service accesses publicly available web content through encrypted network connections and proxy infrastructure.
3. Account Registration and Security
To access the Service, you must create an account by providing accurate, current, and complete information. You are responsible for maintaining the confidentiality of your account credentials and for all activities that occur under your account. You agree to notify us immediately at [email protected] of any unauthorized use of your account.
We reserve the right to suspend or terminate accounts that we reasonably believe are being used in violation of these Terms or the Acceptable Use Policy, with or without prior notice.
4. Subscription Plans and Payment
4.1 Subscription Tiers
The Service is offered on a monthly subscription basis at published pricing tiers. Each tier includes specified limits on concurrent projects, AI processing token budgets, and proxy bandwidth allocations. Current pricing and tier details are available on our website at axiomisr.com.
4.2 Billing
All payments are processed through Stripe, Inc. By subscribing, you authorize us to charge your designated payment method on a recurring monthly basis. All fees are quoted and charged in United States Dollars (USD) unless otherwise specified.
4.3 Price Changes
We may modify subscription pricing with thirty (30) days’ prior written notice. Price changes will take effect at the beginning of the next billing cycle following the notice period. Continued use of the Service after a price change constitutes acceptance of the new pricing.
4.4 Failed Payments
If a payment fails, we will attempt to process the charge up to three (3) additional times over a fourteen (14) day period. If all payment attempts fail, your account will be suspended. During suspension, active investigation processes will be stopped, but your data will be retained for a period of seven (7) days. Service will be restored upon successful payment.
4.5 Refunds
Subscription fees are generally non-refundable. If the Service experiences a material failure rendering it substantially unusable for a period exceeding seventy-two (72) consecutive hours, you may request a prorated credit for the affected period by contacting [email protected]. Credits will be applied to your next billing cycle. No cash refunds will be issued.
5. Customer Data and Ownership
5.1 Your Data
You retain all ownership rights to the data you input into the Service (investigation goals, project configurations, manually collected URLs) and to the investigation outputs generated by the Service on your behalf (intelligence objects, relationship maps, executive summaries, and exported reports). We claim no ownership over your investigation data.
5.2 Collected Web Content
The Service collects and processes publicly available web content as part of its investigation function. This content is stored within your dedicated server instance and is not shared with other customers or used by us for any purpose other than providing the Service to you. Publicly available content collected by the Service may be subject to the intellectual property rights of third parties. You are solely responsible for your use of such content. You acknowledge that third-party websites may have terms of service prohibiting automated access or scraping. You are solely responsible for compliance with any third-party terms. We expressly disclaim any liability arising from your violation of third-party terms of service.
5.3 Dedicated Infrastructure
Each Customer account operates on a dedicated, isolated server instance. Your investigation data, collected content, and AI-generated analysis are stored exclusively on your instance. No other customer can access your data, and your data is not commingled with that of any other customer.
6. Artificial Intelligence Processing
6.1 Third-Party AI Models
The Service uses third-party AI models (including but not limited to Google Gemini) to normalize, analyze, and synthesize collected intelligence. These models are accessed via API and are subject to the terms and pricing of their respective providers. We do not control and are not responsible for the outputs of these AI models.
6.2 No Guarantee of Accuracy
AI-generated outputs, including entity extraction, relationship mapping, executive summaries, and certainty scores, are provided on an “as-is” basis. We do not warrant the accuracy, completeness, or reliability of any AI-generated analysis. The Service is a tool to assist human investigators; it is not a substitute for professional judgment, legal advice, or independent verification of facts.
6.3 Token Budgets
Each subscription tier includes a specified monthly AI processing token budget. Usage is tracked and visible within the Service dashboard. If you exceed your included budget, additional usage may be charged at published overage rates or your AI processing may be paused until the next billing cycle, depending on your plan configuration.
7. Network Infrastructure
The Service accesses publicly available web content through encrypted connections and rotating proxy infrastructure. This architecture is designed to protect the operational security of investigations. The Service only accesses content that is publicly available on the open internet. The Service does not bypass authentication mechanisms, access restricted systems, decrypt protected content, or circumvent technical access controls.
8. Service Availability
We will use commercially reasonable efforts to maintain the availability of the Service. However, the Service is provided without any uptime guarantee or service level agreement (“SLA”). The Service may be unavailable due to scheduled maintenance, emergency maintenance, third-party service outages, force majeure events, or network or infrastructure failures beyond our reasonable control.
We will not be liable for any damages, losses, or consequences arising from Service unavailability.
9. Prohibited Uses and Acceptable Use Policy
Your use of the Service is subject to the Acceptable Use Policy (“AUP”), which is incorporated into these Terms by reference. The AUP defines permitted and prohibited uses of the platform. Violation of the AUP constitutes a material breach of these Terms and may result in immediate suspension or termination of your account without refund.
10. Indemnification
You agree to indemnify, defend, and hold harmless Innovative Technology and Consulting Solutions LLC, its officers, directors, employees, agents, and affiliates from and against any and all claims, demands, liabilities, damages, losses, costs, and expenses (including reasonable attorneys’ fees) arising out of or relating to:
- Your use of the Service, including any investigations conducted using the Service
- Any content you input into or generate through the Service
- Your violation of these Terms or the Acceptable Use Policy
- Your violation of any applicable law, regulation, or third-party right
- Your violation of any third-party terms of service, policies, or access restrictions
- Any claim by a third party related to your investigation activities or use of investigation outputs
- Any unauthorized access to or use of your account
This indemnification obligation shall survive the termination or expiration of these Terms and your use of the Service.
11. Limitation of Liability
11.1 Exclusion of Certain Damages
TO THE MAXIMUM EXTENT PERMITTED BY APPLICABLE LAW, IN NO EVENT SHALL INNOVATIVE TECHNOLOGY AND CONSULTING SOLUTIONS LLC BE LIABLE FOR ANY INDIRECT, INCIDENTAL, SPECIAL, CONSEQUENTIAL, OR PUNITIVE DAMAGES, INCLUDING BUT NOT LIMITED TO LOSS OF PROFITS, LOSS OF DATA, LOSS OF BUSINESS OPPORTUNITY, OR DAMAGE TO REPUTATION, ARISING OUT OF OR RELATING TO YOUR USE OF OR INABILITY TO USE THE SERVICE, REGARDLESS OF THE THEORY OF LIABILITY AND EVEN IF WE HAVE BEEN ADVISED OF THE POSSIBILITY OF SUCH DAMAGES.
11.2 Cap on Liability
TO THE MAXIMUM EXTENT PERMITTED BY APPLICABLE LAW, AND EXCEPT IN CASES OF GROSS NEGLIGENCE OR WILLFUL MISCONDUCT, OUR TOTAL AGGREGATE LIABILITY TO YOU FOR ALL CLAIMS ARISING OUT OF OR RELATING TO THESE TERMS OR THE SERVICE SHALL NOT EXCEED THE TOTAL AMOUNT OF FEES PAID BY YOU TO US DURING THE TWELVE (12) MONTH PERIOD IMMEDIATELY PRECEDING THE EVENT GIVING RISE TO THE CLAIM.
11.3 Basis of the Bargain
THE LIMITATIONS OF LIABILITY SET FORTH IN THIS SECTION REFLECT THE ALLOCATION OF RISK BETWEEN THE PARTIES AND ARE AN ESSENTIAL ELEMENT OF THE BASIS OF THE BARGAIN BETWEEN THE PARTIES. THE SERVICE WOULD NOT BE PROVIDED WITHOUT THESE LIMITATIONS.
12. Disclaimers
THE SERVICE IS PROVIDED “AS IS” AND “AS AVAILABLE” WITHOUT WARRANTIES OF ANY KIND, WHETHER EXPRESS, IMPLIED, STATUTORY, OR OTHERWISE, INCLUDING BUT NOT LIMITED TO IMPLIED WARRANTIES OF MERCHANTABILITY, FITNESS FOR A PARTICULAR PURPOSE, TITLE, AND NON-INFRINGEMENT.
WITHOUT LIMITING THE FOREGOING, WE DO NOT WARRANT THAT: (A) THE SERVICE WILL MEET YOUR REQUIREMENTS; (B) THE SERVICE WILL BE UNINTERRUPTED, TIMELY, SECURE, OR ERROR-FREE; (C) THE RESULTS OBTAINED FROM THE SERVICE WILL BE ACCURATE, RELIABLE, OR COMPLETE; (D) ANY DEFECTS IN THE SERVICE WILL BE CORRECTED; OR (E) THE SERVICE WILL BE COMPATIBLE WITH ANY PARTICULAR HARDWARE, SOFTWARE, OR NETWORK CONFIGURATION.
YOU ACKNOWLEDGE THAT THE SERVICE RELIES ON THIRD-PARTY AI MODELS, THIRD-PARTY PROXY INFRASTRUCTURE, AND PUBLICLY AVAILABLE WEB CONTENT, NONE OF WHICH ARE UNDER OUR EXCLUSIVE CONTROL.
13. Termination
13.1 Termination by Customer
You may cancel your subscription at any time through the Stripe Customer Portal or by contacting [email protected]. Cancellation will take effect at the end of your current billing cycle. No prorated refunds will be issued for partial billing periods.
13.2 Termination by Company
We may suspend or terminate your access to the Service immediately, without prior notice or liability, if: (a) you breach these Terms or the Acceptable Use Policy; (b) your payment is past due for more than fourteen (14) days after all retry attempts; (c) we are required to do so by law, regulation, or court order; or (d) we reasonably believe your use of the Service poses a risk to other customers, our infrastructure, or third parties.
13.3 Effect of Termination
Upon termination or cancellation, your data will be retained on your dedicated server instance for thirty (30) calendar days. During this period, you may request a data export by contacting [email protected]. After thirty (30) days, your server instance and all associated data will be permanently and irreversibly destroyed. We will have no obligation to retain, return, or provide access to your data after the retention period.
14. Governing Law and Dispute Resolution
These Terms shall be governed by and construed in accordance with the laws of the State of Ohio, without regard to its conflict of law principles. Any dispute arising under or relating to these Terms shall be resolved exclusively in the state or federal courts located in Ohio. You consent to the personal jurisdiction of such courts and waive any objection to venue.
15. Modifications to Terms
We reserve the right to modify these Terms at any time. Material changes will be communicated via email at least thirty (30) days before they take effect. Your continued use of the Service after the effective date of any modification constitutes acceptance of the modified Terms. If you do not agree to the modified Terms, your sole remedy is to cancel your subscription before the modification takes effect.
16. General Provisions
Entire Agreement. These Terms, together with the Acceptable Use Policy and Privacy Policy, constitute the entire agreement between you and the Company regarding the Service and supersede all prior agreements, understandings, and communications.
Severability. If any provision of these Terms is held to be invalid, illegal, or unenforceable, the remaining provisions shall continue in full force and effect.
Waiver. Our failure to enforce any right or provision of these Terms shall not constitute a waiver of that right or provision.
Assignment. You may not assign or transfer these Terms or your rights under them without our prior written consent. We may assign these Terms without restriction.
Force Majeure. Neither party shall be liable for any failure or delay in performance due to causes beyond its reasonable control, including but not limited to acts of God, natural disasters, war, terrorism, pandemic, government action, or failure of third-party services.
Contact. For questions about these Terms, contact us at [email protected].
Privacy Policy
Axiom Intelligence Platform — Effective Date: March 29, 2026
1. Introduction
This Privacy Policy describes how Innovative Technology and Consulting Solutions LLC (“Company,” “we,” “us,” or “our”) collects, uses, stores, and protects information in connection with the Axiom Intelligence Platform (the “Service”). This policy applies to all users of the Service (“Customers,” “you,” or “your”).
We are committed to protecting the privacy and security of your information. Please read this policy carefully to understand our practices.
2. Information We Collect
2.1 Account Information
When you create an account, we collect:
- Your name and email address
- Your username and encrypted password (hashed, never stored in plaintext)
- Billing information processed and stored by Stripe, Inc. (we do not directly store credit card numbers)
- Organization name, if provided
2.2 Configuration Data
We store your Service configuration preferences, including:
- AI model preferences and processing budget settings
- API keys you provide for third-party services (encrypted at rest using Fernet symmetric encryption)
- Network configuration preferences (encrypted at rest)
- Project names, descriptions, and investigation goals
2.3 Investigation Data
During the normal operation of the Service, the following data is collected and stored within your dedicated server instance:
- Publicly available web content retrieved during investigations (web pages, news articles, corporate registry data, certificate transparency logs)
- AI-generated intelligence outputs (entity profiles, relationship maps, executive summaries)
- Search terms generated by the AI and used to discover relevant content
- URLs collected and processed
Important: All investigation data is stored exclusively on your dedicated server instance. It is not shared with other customers, not used to train AI models, and not accessed by us except as described in Section 5.
2.4 Usage and Operational Data
We collect limited operational data to maintain the Service:
- AI API token usage and associated costs (for billing and budget enforcement)
- Server health metrics (CPU, memory, disk usage) for monitoring service availability
- Task completion status and error logs for debugging service issues
- Login timestamps and IP addresses for security purposes
2.5 Information We Do NOT Collect
- We do not collect personal information about the subjects of your investigations
- We do not read, review, or analyze the content of your investigations
- We do not use your investigation data to train AI models
- We do not collect biometric data, geolocation data, or device fingerprints
3. How We Use Your Information
We use the information we collect for the following purposes:
- To provide, maintain, and improve the Service
- To process payments and manage your subscription
- To send transactional communications (account confirmation, password resets, payment receipts, service alerts)
- To monitor and enforce compliance with our Terms of Service and Acceptable Use Policy
- To detect, prevent, and respond to security incidents, fraud, or technical issues
- To comply with legal obligations, including responding to valid legal process
4. Data Storage and Security
4.1 Dedicated Server Architecture
Each Customer’s data is stored on a dedicated, isolated server instance hosted by DigitalOcean, Inc. (or other hosting providers as specified). Your instance is not shared with any other customer. Database credentials, encryption keys, and API keys are unique to your instance and encrypted at rest.
4.2 Encryption
- Sensitive configuration data (API keys, network credentials) is encrypted at rest using Fernet symmetric encryption derived from a per-instance secret key
- All data in transit between your browser and the Service is encrypted using TLS 1.2 or higher
- All outbound investigation traffic is encrypted in transit
- Database passwords are generated per-instance and not shared
4.3 Backups
Automated daily database backups are stored in encrypted object storage (Backblaze B2 or equivalent) in a separate account from your server instance. Backups are retained for thirty (30) days and then permanently deleted. Backup storage is encrypted at rest by the storage provider.
4.4 Security Measures
We implement industry-standard security measures including but not limited to:
- Firewall rules restricting access to necessary ports only
- SSH key-based authentication for server administration (no password-based SSH)
- Automated monitoring and alerting for server health and availability
- Regular security updates applied to server operating systems and dependencies
5. Who Can Access Your Data
Access to your dedicated server instance is restricted to:
- You: Through the web-based Service interface using your account credentials.
- Our authorized personnel: Only for infrastructure-level maintenance, troubleshooting, or updating the Service infrastructure. We do not access, review, or analyze the content of your investigations. If technical support requires accessing your specific investigation data, we will obtain your explicit written permission prior to access.
- Law enforcement: Only in response to valid legal process (subpoena, court order, or warrant) as described in Section 7.
We do not sell, rent, lease, or share your data with any third party for commercial purposes.
6. Third-Party Service Providers
The Service uses the following third-party providers to operate. Each processes limited data as necessary for their function:
- Stripe, Inc.: Payment processing. Receives your payment method details and billing information. Subject to Stripe’s Privacy Policy.
- Google (Gemini API): AI processing. Receives investigation text for analysis. Subject to Google’s API Terms. We do not send your personal account information to Google.
- DigitalOcean, Inc.: Server hosting. Provides the infrastructure on which your dedicated instance runs. Subject to DigitalOcean’s Privacy Policy.
- Commercial proxy providers: Route investigation web traffic. See only destination URLs and traffic volume, not investigation context or your identity.
- Resend (or equivalent): Transactional email delivery. Receives your email address for sending account-related communications.
- Backblaze B2 (or equivalent): Encrypted backup storage. Stores encrypted database backups.
7. Law Enforcement and Legal Requests
We will disclose your information to law enforcement or government authorities only when required to do so by valid legal process, including a lawfully issued subpoena, court order, or search warrant. When legally permitted, we will notify you of such requests before disclosing your information.
We will not voluntarily provide your investigation data to any law enforcement agency or government authority without valid legal process, except where we have a good faith belief that disclosure is necessary to prevent imminent serious physical harm or death.
8. Geographic Restrictions and GDPR
The Service is currently intended for use by individuals and entities located within the United States. We do not market the Service to, nor do we intentionally collect or process the personal data of, individuals residing in the European Economic Area (EEA), United Kingdom, or Switzerland subject to the General Data Protection Regulation (GDPR).
9. Data Retention
- Active accounts: Your data is retained on your dedicated server instance for the duration of your subscription.
- After cancellation: Your server instance and all data are retained for thirty (30) calendar days after cancellation to allow data export. After this period, the instance and all data are permanently destroyed.
- After termination for cause: If your account is terminated for violation of the Terms of Service or AUP, we may retain your data for up to ninety (90) days for evidentiary purposes before permanent destruction.
- Backups: Automated backups are retained for thirty (30) days and then permanently deleted.
- Billing records: Payment records are retained by Stripe in accordance with their data retention policies and applicable tax and financial record-keeping laws.
10. Children’s Privacy
The Service is not intended for use by individuals under the age of eighteen (18). We do not knowingly collect personal information from children under 18. If we become aware that a child under 18 has provided us with personal information, we will take steps to delete such information. Additionally, as specified in the Acceptable Use Policy, intentionally investigating minors is a prohibited use of the Service.
11. Changes to This Privacy Policy
We may update this Privacy Policy from time to time. Material changes will be communicated via email at least thirty (30) days before they take effect. The “Effective Date” at the top of this policy will be updated to reflect the date of the most recent revision. Continued use of the Service after the effective date constitutes acceptance of the updated Privacy Policy.
Contact. For questions, concerns, or requests related to this Privacy Policy or your personal data, contact us at:
Innovative Technology and Consulting Solutions LLC
Email: [email protected]
Support: [email protected]
Acceptable Use Policy
Axiom Intelligence Platform — Effective Date: March 29, 2026
1. Purpose
This Acceptable Use Policy (“AUP”) defines the permitted and prohibited uses of the Axiom Intelligence Platform (the “Service”) operated by Innovative Technology and Consulting Solutions LLC (the “Company”). This AUP is incorporated by reference into the Terms of Service and applies to all users of the Service. Violation of this AUP may result in immediate suspension or termination of your account without refund.
2. Permitted Uses
The Service is designed for lawful open-source intelligence (OSINT) research and investigation activities conducted using publicly available information. Permitted uses include but are not limited to:
- Corporate due diligence and background investigations using public records and media
- Fraud investigation and asset tracing using publicly available data
- Compliance research, including sanctions screening, PEP identification, and anti-money laundering inquiries
- Investigative journalism and public interest research
- Security and threat intelligence analysis using open sources
- Academic and policy research
- Law enforcement and government intelligence analysis conducted under lawful authority
- Competitive intelligence using publicly available business information
3. Prohibited Uses
You must not use the Service for any of the following purposes. This list is illustrative and not exhaustive. We reserve the right to determine, in our sole discretion, whether a particular use violates this AUP.
3.1 Illegal Activities
- Any activity that violates applicable federal, state, local, or international law or regulation
- Any activity that would constitute a criminal offense or give rise to civil liability
- Unauthorized access to computer systems, networks, or data (including any attempt to bypass authentication, exploit vulnerabilities, or access non-public systems)
- Any activity that violates the Computer Fraud and Abuse Act (18 U.S.C. § 1030), the Stored Communications Act (18 U.S.C. § 2701), or equivalent laws in any jurisdiction
3.2 Harassment, Stalking, and Harm to Individuals
- Stalking, monitoring, or surveilling any individual without lawful authority
- Harassment, intimidation, threats, or any activity intended to cause fear or harm
- Investigating, tracking, or monitoring current or former intimate partners, family members, or other individuals for personal, non-professional purposes
- Intentionally targeting or investigating minors (individuals under 18 years of age) for any purpose. (Incidental collection of public data referencing minors during a lawful, broadly targeted investigation is not a violation).
- Doxxing: collecting and publishing private or identifying information about individuals with the intent to harass, threaten, or facilitate harm
- Any use that facilitates domestic violence, abuse, or coercive control
3.3 Discrimination and Prohibited Screening
- Using investigation results to make or inform decisions about an individual’s eligibility for employment, housing, credit, insurance, education, or public accommodations in violation of applicable anti-discrimination laws
- Any use that constitutes a consumer report under the Fair Credit Reporting Act (FCRA) without compliance with FCRA requirements. The Service is not a consumer reporting agency and does not provide consumer reports. No marketing materials, sales communications, or implied capabilities of the Service supersede this strict prohibition.
3.4 Interference with Third-Party Systems
- Intentionally overloading, disrupting, or degrading any third-party website or service through the Service
- Circumventing, disabling, or interfering with security-related features of any website or service
- Accessing content behind paywalls, login walls, or other access controls
3.5 Misrepresentation and Fraud
- Creating false or misleading intelligence reports and representing them as factual
- Fabricating evidence or manipulating investigation outputs for use in legal, regulatory, or administrative proceedings
- Impersonating any person or entity, or falsely representing your affiliation with any person or entity
3.6 Platform Abuse
- Attempting to access other customers’ server instances, data, or accounts
- Reverse-engineering, decompiling, or disassembling the Service software
- Using the Service to develop a competing product or service
- Reselling, sublicensing, or providing access to the Service to third parties without written authorization
- Sharing account credentials with unauthorized individuals
- Deliberately generating excessive AI processing load to consume resources beyond your plan allocation
4. Customer Responsibilities
As a user of the Service, you are responsible for:
- Ensuring that your use of the Service complies with all applicable laws and regulations in your jurisdiction
- Obtaining any required authorizations, licenses, or legal opinions before conducting investigations that may implicate privacy, data protection, or surveillance laws
- Independently verifying the accuracy of investigation outputs before relying on them for any purpose, including legal, financial, regulatory, or employment decisions
- Maintaining the security of your account credentials and server instance
- Promptly notifying us at [email protected] if you become aware of any use of the Service that violates this AUP
5. Enforcement
We reserve the right to investigate suspected violations of this AUP and to take any action we deem appropriate, including:
- Issuing warnings to the account holder
- Temporarily suspending the account and stopping all investigation processes
- Permanently terminating the account and destroying all associated data
- Reporting suspected illegal activity to appropriate law enforcement authorities
- Cooperating with law enforcement investigations pursuant to valid legal process
Enforcement decisions are made in our sole discretion. We are not obligated to provide advance notice before taking enforcement action in cases of serious or ongoing violations.
6. Reporting Violations
If you become aware of any use of the Service that violates this AUP, or if you believe you have been harmed by another customer’s use of the Service, please report it to [email protected]. We will investigate all credible reports and take appropriate action.
7. Changes to This Policy
We may update this AUP from time to time. Material changes will be communicated via email at least thirty (30) days before they take effect. Continued use of the Service after the effective date constitutes acceptance of the updated AUP.